ScreenShot
| Created | 2025.03.28 15:15 | Machine | s1_win7_x6402 |
| Filename | sfmw.hta | ||
| Type | HTML document, ASCII text, with very long lines, with CRLF line terminators | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 3 detected () | ||
| md5 | f32e7891e2cfc58230057a506325c3c8 | ||
| sha256 | 02783530bbd8416ebc82ab1eb5bbe81d5d87731d24c6ff6a8e12139a5fe33cee | ||
| ssdeep | 3072:UPzcBmc2YlnFBQsDqzpj8sfZCQiItHU/j1ICbM+33Eci:Acz29RNxY71ICAG3Eci | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (11cnts)
| Level | Description |
|---|---|
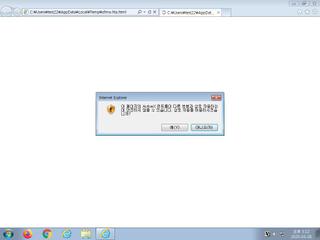
| watch | A command shell or script process was created by an unexpected parent process |
| watch | Creates a suspicious Powershell process |
| watch | One or more non-whitelisted processes were created |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | A process created a hidden window |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Creates a suspicious process |
| notice | File has been identified by 3 AntiVirus engines on VirusTotal as malicious |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
Rules (9cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | PowerShell | PowerShell script | scripts |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|