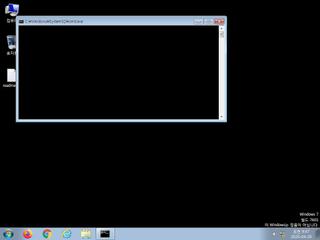
ScreenShot
| Created | 2025.04.29 09:50 | Machine | s1_win7_x6401 |
| Filename | test.pdf.lnk | ||
| Type | MS Windows shortcut, Item id list present, Has Relative path, Has command line arguments, Icon number=11, ctime=Sun Dec 31 15:32:08 1600, mtime=Sun Dec 31 15:32:08 1600, atime=Sun Dec 31 15:32:08 1600, length=0, window=hidenormalshowminimized | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | 32 detected (Pantera, Save, gen111, LNKEXEC, GenBadur, genw, Mshta, CLASSIC, DownLoader48, DownLnk, Static AI, Suspicious LNK, Detected, WinLNK, HNDC, ABTrojan, BZCW, Artemis, Link, Crafted, Probably Heur, LNKScript, Yimw) | ||
| md5 | 3b4cbac8dad90d932e233a89650530a0 | ||
| sha256 | d8fe935ffee91b6d589392e60c0af2c0de956b21fa9b752a468bbbff6a495afe | ||
| ssdeep | 24:8Ayw/BHYVKVWO+/CWX62fV46/KkDdd79dsoEZ/7QAMN5:8y5aj62fV4YdJ9ha7Q | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (21cnts)
| Level | Description |
|---|---|
| danger | The process powershell.exe wrote an executable file to disk which it then attempted to execute |
| danger | File has been identified by 32 AntiVirus engines on VirusTotal as malicious |
| watch | A command shell or script process was created by an unexpected parent process |
| watch | Communicates with host for which no DNS query was performed |
| watch | Disables proxy possibly for traffic interception |
| watch | Found URLs in memory pointing to an IP address rather than a domain (potentially indicative of Command & Control traffic) |
| watch | One or more non-whitelisted processes were created |
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates a shortcut to an executable file |
| notice | Creates a suspicious process |
| notice | HTTP traffic contains suspicious features which may be indicative of malware related traffic |
| notice | Performs some HTTP requests |
| notice | Potentially malicious URLs were found in the process memory dump |
| notice | Yara rule detected in process memory |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (36cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (upload) |
| watch | Antivirus | Contains references to security software | binaries (upload) |
| watch | Network_Downloader | File Downloader | memory |
| notice | Code_injection | Code injection with CreateRemoteThread in a remote process | memory |
| notice | Create_Service | Create a windows service | memory |
| notice | Escalate_priviledges | Escalate priviledges | memory |
| notice | Generic_PWS_Memory_Zero | PWS Memory | memory |
| notice | KeyLogger | Run a KeyLogger | memory |
| notice | local_credential_Steal | Steal credential | memory |
| notice | Network_DGA | Communication using DGA | memory |
| notice | Network_DNS | Communications use DNS | memory |
| notice | Network_FTP | Communications over FTP | memory |
| notice | Network_HTTP | Communications over HTTP | memory |
| notice | Network_P2P_Win | Communications over P2P network | memory |
| notice | Network_TCP_Socket | Communications over RAW Socket | memory |
| notice | ScreenShot | Take ScreenShot | memory |
| notice | Sniff_Audio | Record Audio | memory |
| notice | Str_Win32_Http_API | Match Windows Http API call | memory |
| notice | Str_Win32_Internet_API | Match Windows Inet API call | memory |
| info | anti_dbg | Checks if being debugged | memory |
| info | antisb_threatExpert | Anti-Sandbox checks for ThreatExpert | memory |
| info | Check_Dlls | (no description) | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerCheck__RemoteAPI | (no description) | memory |
| info | DebuggerException__ConsoleCtrl | (no description) | memory |
| info | DebuggerException__SetConsoleCtrl | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | lnk_file_format | Microsoft Windows Shortcut File Format | binaries (upload) |
| info | Lnk_Format_Zero | LNK Format | binaries (upload) |
| info | PowerShell | PowerShell script | scripts |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
| info | win_hook | Affect hook table | memory |