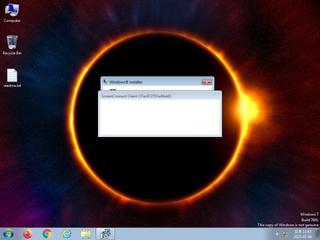
ScreenShot
| Created | 2025.05.04 13:07 | Machine | s1_win7_x6403 |
| Filename | 8e22440b-0bf6-4a02-bfa9-d9f1fd71f8c5 | ||
| Type | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : malware | ||
| VT API (file) | 60 detected (AIDetectMalware, AsyncRat, Ghanarava, Jalapeno, Unsafe, Save, malicious, confidence, 100%, gen1, high confidence, MalwareX, Dapato, kwtdfr, MSIL@AI, MSIL2, g0OJ+e+r5mmFCwNkugBx3w, MulDrop23, AMADEY, YXFDOZ, Real Protect, high, score, Mdrop, Static AI, Malicious PE, bmnl, Detected, GrayWare, Wacapew, Malware@#32iysi6dssiy0, ABJU, Eldorado, Artemis, TScope, GdSda, PE04C9Z, MkkPSPTXLQ, susgen, AKUI3DGW) | ||
| md5 | 22ebc0313c30af0f2610460f763b56b6 | ||
| sha256 | de01202c6aac1f0e971e018ef0f592f440f0dd0a62a955f514d27cdf63e5edcd | ||
| ssdeep | 393216:lFdm2pcQiNyeHA2gjLlrlF+7r0IuW5vuewmn2AM:lFdm2pwNlHA2oTF+EIu6vtlM | ||
| imphash | f34d5f2d4577ed6d9ceec516c1f5a744 | ||
| impfuzzy | 3:rGsLdAIEK:tf | ||
Network IP location
Signature (16cnts)
| Level | Description |
|---|---|
| danger | File has been identified by 60 AntiVirus engines on VirusTotal as malicious |
| danger | Executed a process and injected code into it |
| watch | A process performed obfuscation on information about the computer or sent it to a remote location indicative of CnC Traffic/Preperations. |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Checks for the Locally Unique Identifier on the system for a suspicious privilege |
| notice | Creates executable files on the filesystem |
| notice | Drops a binary and executes it |
| notice | Drops an executable to the user AppData folder |
| notice | Queries the disk size which could be used to detect virtual machine with small fixed size or dynamic allocation |
| notice | The binary likely contains encrypted or compressed data indicative of a packer |
| info | Checks amount of memory in system |
| info | Checks if process is being debugged by a debugger |
| info | Collects information to fingerprint the system (MachineGuid |
| info | One or more processes crashed |
| info | Queries for the computername |
| info | Uses Windows APIs to generate a cryptographic key |
Rules (15cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| warning | Generic_Malware_Zero | Generic Malware | binaries (download) |
| watch | Antivirus | Contains references to security software | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (download) |
| watch | Malicious_Library_Zero | Malicious_Library | binaries (upload) |
| watch | UPX_Zero | UPX packed file | binaries (download) |
| info | CAB_file_format | CAB archive file | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (download) |
| info | Is_DotNET_EXE | (no description) | binaries (upload) |
| info | IsDLL | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (download) |
| info | IsPE32 | (no description) | binaries (upload) |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (download) |
| info | OS_Processor_Check_Zero | OS Processor Check | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (download) |
| info | PE_Header_Zero | PE File Signature | binaries (upload) |
PE API
IAT(Import Address Table) Library
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none
mscoree.dll
0x402000 _CorExeMain
EAT(Export Address Table) is none