ScreenShot
| Created | 2025.05.04 22:53 | Machine | s1_win7_x6401 |
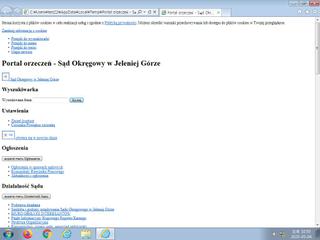
| Filename | Portal orzeczeń - Sąd Okręgowy w Jeleniej Górze.html | ||
| Type | HTML document, UTF-8 Unicode text, with very long lines | ||
| AI Score | Not founds | Behavior Score |
|
| ZERO API | file : clean | ||
| VT API (file) | |||
| md5 | 8f98cdc0f13e4db7f76b3e3bfa7e8264 | ||
| sha256 | 775e4159d4c94e78212fa25839d90be0fe4ee231cbf04aaf58132bccd2dc4ba0 | ||
| ssdeep | 384:Jm+ho62LuE8xQJXL2O8KXJDjyLgEegUeLCeLT/7V:Jm62SE8x+L2O8KXJ6LgdgtL3Lr7V | ||
| imphash | |||
| impfuzzy | |||
Network IP location
Signature (5cnts)
| Level | Description |
|---|---|
| watch | Resumed a suspended thread in a remote process potentially indicative of process injection |
| notice | Allocates read-write-execute memory (usually to unpack itself) |
| notice | Changes read-write memory protection to read-execute (probably to avoid detection when setting all RWX flags at the same time) |
| notice | Uses Windows utilities for basic Windows functionality |
| notice | Yara rule detected in process memory |
Rules (9cnts)
| Level | Name | Description | Collection |
|---|---|---|---|
| info | anti_dbg | Checks if being debugged | memory |
| info | DebuggerCheck__GlobalFlags | (no description) | memory |
| info | DebuggerCheck__QueryInfo | (no description) | memory |
| info | DebuggerHiding__Active | (no description) | memory |
| info | DebuggerHiding__Thread | (no description) | memory |
| info | disable_dep | Bypass DEP | memory |
| info | Microsoft_Office_File_Zero | Microsoft Office File | binaries (download) |
| info | SEH__vectored | (no description) | memory |
| info | ThreadControl__Context | (no description) | memory |
Network (0cnts) ?
| Request | CC | ASN Co | IP4 | Rule ? | ZERO ? |
|---|
Suricata ids
SSLBL: Malicious JA3 SSL-Client Fingerprint detected (Tofsee)